Since the pandemic, employers around the world have needed to change. They’ve had to shift how their employees operate. Remote work is very much here to stay. Organizations and employees can both benefit from the work-from-home and hybrid work revolution.
Cost savings is a driver for supporting remote work. Employee morale and productivity also can be higher when employers grant this flexibility.
A majority of organizations support some type of remote work. Statistics show that:
- 16% of companies are completely remote
- 40% support hybrid office/remote working
- 44% don’t allow employees to work remotely
While there are benefits, there are also challenges to this new environment. Employers worry about the cybersecurity risks of remote teams. Managers can find it more challenging to make sure employees are doing what they should do.
The remote and hybrid work environment has led to the rise of employee monitoring tools. These tools have mixed reviews from employees.
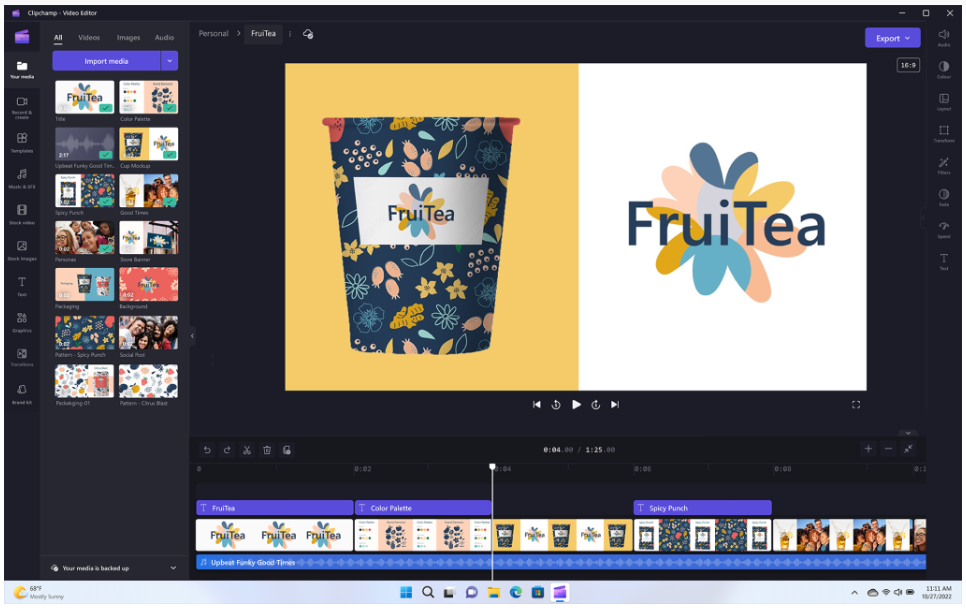
What Is Employee Monitoring Software?
Employee monitoring software tracks digital movements. This can include everything from general clock-in clock-out tracking to taking screenshots of an employee’s computer several times per hour.
Tracking tools like Hubstaff and BambooHR track many activities on a person’s computer. The information is then sent in a daily or weekly report to the company.
Items that these tools can track are:
- Time clock
- Keyboard activity
- Keystrokes
- Mouse activity
- Websites visited
- Screenshots of the desktop
- Apps used and how long in use
The most invasive of tools can even track the sounds and video of the employee. Tracking can be visible, so the employee knows about it or hidden from the employee. It depends on the tool used and the ethical considerations of the employer.
This type of monitoring can benefit an organization worried about “productivity theft.” But it can also alienate good employees and torpedo morale and trust. We’ll go through the pros and cons to weigh before you set up this type of system.
Pros of Activity Monitoring Tools
Helps Managers Understand How Employees Spend Their Day
One feature of many tracking tools is the ability to track time by project. This helps managers understand where employees are prioritizing their time. Knowing how much time employees spend on a project helps with ROI projections.
Reduces Non-Work Activities During Working Hours
One thing that employers worry about with remote employees is that they will waste time. A manager doesn’t want to pay someone only to find out the employee spent half their time on Facebook.
About half of monitored employees spend 3+ hours per day on non-work activities. When employees know that their boss is monitoring their app usage, they’re less likely to goof off.
Can Be an Easy Way to Track Time for Remote Workers
Smaller companies that work with fully remote teams may find tracking tools convenient. Employees or freelancers can track their time at the click of a button. Employers can put an hour-per-week cap on time. They can also manage payments automatically through the app.
Cons of Activity Monitoring Tools
Hurts Employees’ Morale & Productivity
Many employees feel they are put in a cage when monitoring is introduced. Morale can plummet, which takes productivity along with it.
Instead of focusing on work completely, various thoughts go through employees’ minds. Such as, “If I think about this problem too long, is the tracking going to give me a low productivity score?” Or “What happens when I’m on the phone with a customer and not moving my mouse around? Will the tracking make it look like I’m not working?”
Some of the feelings that employees can have when monitored are:
- Betrayed
- No longer trusted
- Loss of company loyalty
- Hurt
- Treated like a number instead of a person
“Activity Monitoring” Doesn’t Mean Productivity
Many of these tracking tools send employees and employers “activity reports.” These reports simply look at keyboard and mouse activity during a specific time.
But what if the employee must solve a workflow issue and needs to use their brain, not the mouse? What if a salesperson is on the phone with a customer, not using their keyboard? Zoom calls bring a similar quandary. If you’re in a Zoom call, your mouse and keyboard aren’t being actively used as they would if you are typing.
Yet, the activity report doesn’t include this information. It will simply give a score of x% based on keyboard and mouse activity. This could make an employer think a worker was goofing off when they were actually working hard.
Costs Organizations Good Employees
Nearly half (47%) of surveyed tech employees stated they would quit if their boss tracked them. Employers implementing monitoring can alienate good employees and make them feel untrusted. They can also feel unappreciated.
When you relegate everyone to a number of keyboard strokes, you constrain creativity. Good employees often stay with companies where they feel appreciated and can grow. Once that’s gone, they’re likely to leave.
Finding a Balance
A few things to think about when finding the right balance between tracking too much or too little are:
- What do you really need to track?
- Should you treat all employees the same?
- What do your employees think about monitoring?
- Are you trying to solve a problem that doesn’t exist?
- What features are unnecessary that you can turn off?
- Is the tool giving you accurate data related to productivity?
Get Expert Advice on the Best Tools for Your Business
Cloud tools are an important part of your business. You should deploy them thoughtfully. Contact us today to schedule a chat and get valuable advice.
This Article has been Republished with Permission from The Technology Press.